Organizations today rely heavily on Microsoft 365 to manage their productivity and security needs. With multiple services and applications offered within the Microsoft 365 suite, it’s crucial for organizations to manage permissions and security settings effectively. In this article, we will delve into the Microsoft 365 permission model, specifically focusing on the Azure Role-Based Access Control (Azure RBAC) and its relationship with the Microsoft 365 Defender portal.
Azure RBAC serves as the foundation for the Microsoft 365 permission model. It simplifies the process of assigning permissions by allowing administrators to assign predefined roles to users instead of assigning individual permissions. This approach enhances efficiency and makes permission management more effective.
In Microsoft 365, administrative roles for all products can be managed through Azure Active Directory. Azure RBAC enables administrators to assign roles to users, with each role containing predefined permissions. This means that instead of granting multiple permissions individually, you can assign a role that encapsulates the necessary permissions for specific tasks. This streamlines the process and reduces the potential for error.
Microsoft 365 offers a variety of predefined administrator roles that correspond to common business functions. These roles provide individuals in your organization with specific permissions to perform tasks within the Microsoft 365 admin centre. It’s essential to carefully plan and assign these roles to responsible and trustworthy individuals.
Users must have the appropriate access level to manage permissions in the Microsoft 365 Defender portal. Global administrators or Organization Management role group members in the Microsoft 365 Defender portal can manage permissions. Specifically, the Role Management role grants users the ability to view, create, and modify role groups within the portal. By default, this role is assigned only to the Organization Management role group.
It’s worth noting that other online services within Microsoft 365 have their own permission models. For instance, Exchange Online adopts a similar Azure RBAC model to define administrator roles, but it also employs a security model based on individual permissions for mailboxes. On the other hand, SharePoint Online has its own security permission model centred around security groups, permissions, and permission levels. These models allow administrators to assign permissions at different levels within SharePoint, such as site collections, sites, and documents.
The permission structure in the Microsoft 365 Defender portal aligns with the RBAC permissions model used across most Microsoft 365 services. If you are already familiar with the permission structure in these services, granting permissions in the Defender portal will be intuitive. The RBAC model revolves around two key components: roles and role groups.
A role defines a set of tasks and permissions granted to users. A role group, on the other hand, comprises a collection of roles that enable individuals to perform their duties within the Microsoft 365 Defender portal. By default, the portal includes various default role groups designed to address common tasks and functions. It is recommended that organizations add individual users as members to these default role groups.
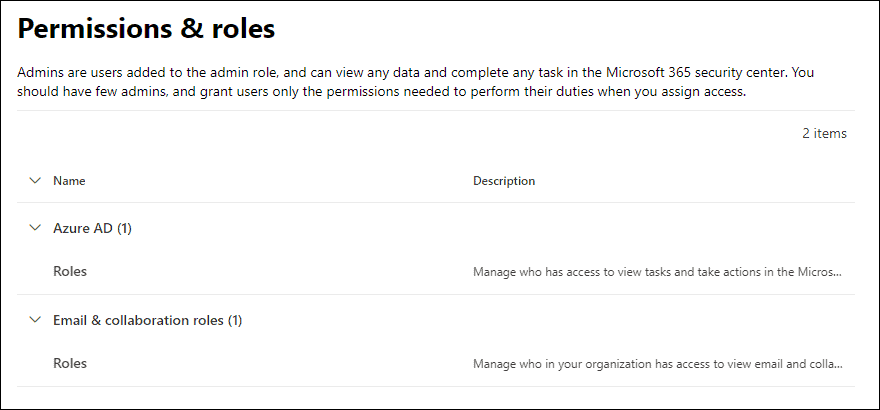
Within the Microsoft 365 Defender portal, you will encounter different types of roles and role groups on the Permissions & Roles page:
- Azure AD roles: These central roles assign permissions for all Microsoft 365 services. While you can view these roles and assigned users in the Microsoft 365 Defender portal, managing the roles themselves is done through Azure AD.
- Email and collaboration roles: These roles specifically pertain to the Microsoft 365 Defender portal and the Microsoft 365 compliance centre. It’s important to note that these roles do not encompass all the permissions required for other Microsoft 365 workloads. Each online service, such as Exchange Online and SharePoint Online, has its own permission models, and their service-specific roles are managed through their respective portals.
Understanding the Microsoft 365 permission model is crucial for organizations to manage security and effectively assign appropriate access levels to users. By leveraging the Azure RBAC and utilizing the Microsoft 365 Defender portal, organizations can centrally manage permissions and ensure that the right people have the necessary access to perform security tasks.
The following screenshot displays the Permissions & roles page in the Microsoft 365 Defender portal.
Credit: Microsoft
Additional reading. For more information on all the Azure RBAC roles available in Microsoft 365, see the following article about Office 365 admin roles.
